Besuchen Sie unseren neuen Webshop für weitere Produkte: stealth-phones.com
Besuchen Sie unseren deutschen Händler: https://www.anti-interception.com/
Über XCell Stealth Handys und
GSM Abhörtechnik
Was ist IMEI, A5 und GSM Localization?
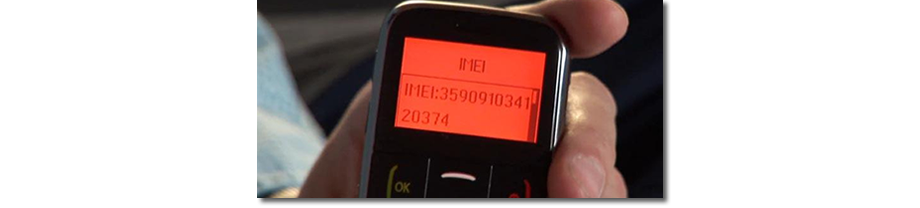
The International Mobile Station Equipment Identity or IMEI is a number, usually unique, used by a GSM network to identify valid devices. It is also used by IMEI/IMSI catchers / GSM interceptors in order to identify your phone and performing call interception.
The GSM ciphering algorithm is called A5. It can be supressed (active and semi active GSM interceptors) or broken (passive GSM interceptors) in order to eavesdrop your phone calls and SMS. Also, it can be supressed by GSM carrier due to a warrant.
GSM Localization: referring to how the cell towers which receive a phone's signal may be used to calculate its geophysical location. Same technique is used if instead of cell tower the phone is connected to a GSM interceptor. Invizible interrogation messages (called Ping) will be sent to your phone, in order to calculate its location.
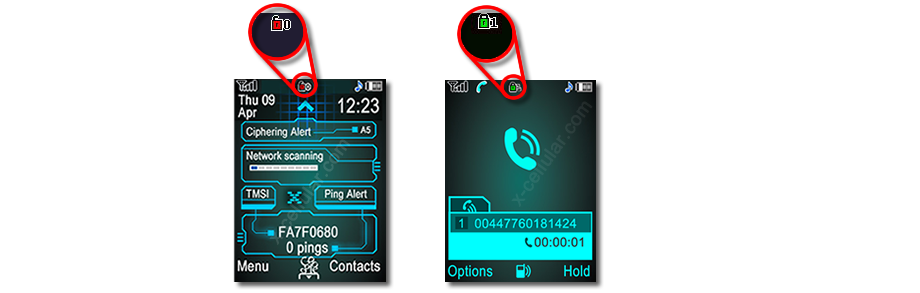
All changes of above identifiers and parameters are instantly detected by XCell Stealth Phones, which will warn you every time when such intrusion attempts are in progress.
Can you really trust your cell phone?
A mobile phone is really a tracking device that lets you make calls. Over the past decades, telecommunication interception has developed into a huge worldwide industry allowing a phone to be bugged remotely. Most interception of mobile communications is made during the call, the equipment used is very advanced, commonly referred to as a GSM interceptor. These systems are used by many special security organizations for security purposes, however this may not always be the case. Different foreign and local agencies, security organisations within almost all countries routinely intercept calls and are able to bug a cell phone remotely that may yield sensitive political, military, economic or simply private information. The use of wiretapping has become so widespread, simple and uncontrolled that you should assume that records of you private calls end up in the wrong hands.
Identifying IMEI and IMSI
Every mobile phone has the requirement to optimize the reception. If there is more than one base station of the subscribed network operator accessible, it will always choose the one with the strongest signal. An IMSI/IMEI-catcher masquerades as a base station and causes every mobile phone of the simulated network operator within a defined radius to log in. With the help of a special identity request, it is able to force the transmission of the IMEI and IMSI. Tricking the mobile phones has been always pretty easy, as long as the phone is not asking the network for authentication, but only vice versa. GSM interceptors (IMEI/IMSI catchers) uses BCCH manipulation to give a "virtual power" effect of up to several hundred watts. By doing that, a GSM interceptor will trick the handsets, which will always choose the "BTS" with the strongest signal. As well, by changing Cell ID (all other network parameters remains the same - MCC, MNC, LAC) and ARFCN, the interceptor forces the cell phones within the area to send registration requests, collecting this way phone identifiers: IMSI, IMEI, classmark etc.
Tapping a mobile phone
The IMEI/IMSI catcher (or GSM interceptor) subjects the phones in its vicinity to a man-in-the-middle attack, acting to them as a preferred base station in terms of signal strength. With the help of a SIM, it simultaneously logs into the GSM network as a mobile station. Since the encryption mode is chosen by the base station, the IMEI/IMSI-catcher can induce the mobile station to use no encryption at all. Hence, it can encrypt the plain text traffic from the mobile station and pass it to the base station.
The "Ciphering Indication Feature" is suppressed by the network provider by setting the OFM (Operational Feature Monitor) bit in the "administrative data" field (EFAD, see GSM 11.11, 10.3.18) on the SIM card, in order to make IMEI/IMSI catchers (GSM interceptors) invisible for the phone user. Usually the Ciphering Indicator is turned off and you cannot modify the administrative data in the SIM. But XCell Stealth Phones are bypassing that provider settings and warns the phone user in case of interception.

The interceptor can be programmed to see any phone call by catching the IMEI number of the phone then monitoring the phone as well as locking onto the cell transmission during the call, the interceptor can then de crypt and manipulate the encoded transmission from your phone to the relevant BTS tower (base transceiver station). This will allow the interceptor operator to listen into your phone call as well as send or receive all your text message correspondence totally anonymously and remotely with no need for physically contact of your mobile phone or handset.
The GSM interceptor uses an active system that captures the IMEI of the targets by acting like a fake base station (BTS).
The GSM interceptor initializes the operation of the false base station. Thus, one fake cell is formed for which the MCC, MNC and ARFCN values will correspond to the parameters of a cell communication operator, operating in a given district, and the LAC is set to a different value from what is used in the real network. This operation is called handover forcing: the mobile phones, which are within its operation radius, will acknowledge activation of a strong channel and will start the registration procedure. They will transmit to the interceptor their IMEI, TMSI (received in real GSM networks), class mark, KcN. For the subscribers (cell phones), registration in the fake network does not differ from registration in the real operator network.
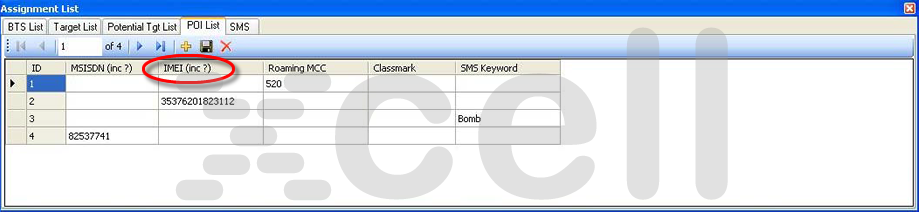
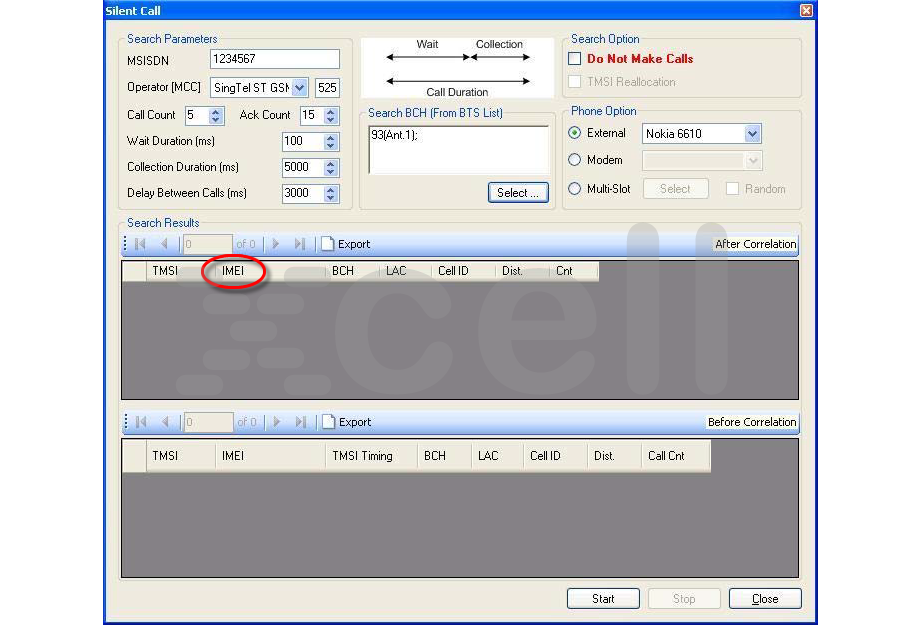
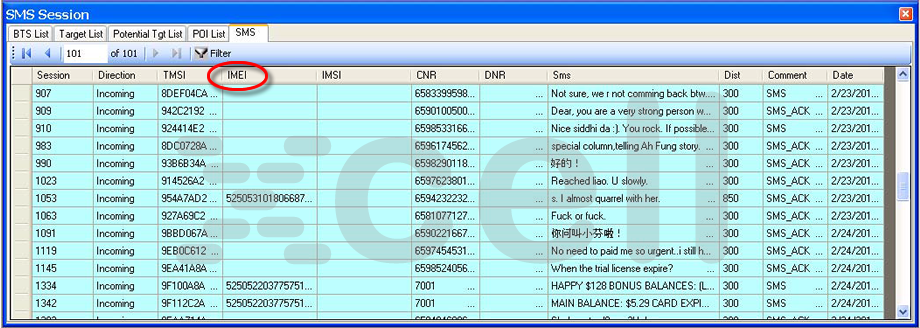
Below you can see few interception procedures, gathering phones IMEI details and then using IMEI for listening on active calls, intercepting SMS etc.
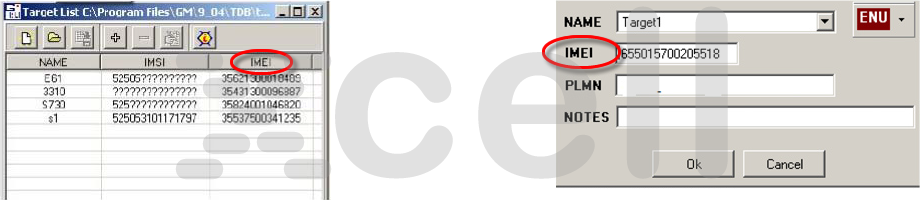
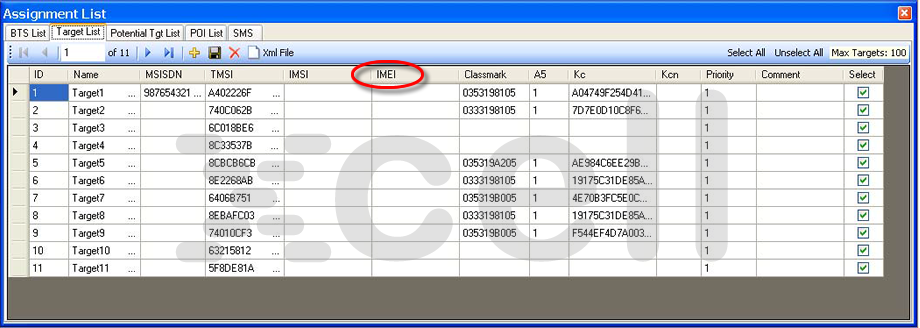
The system operates in Random mode as well as in Target mode. It can filter, track and record only the target operation.
In Random mode interception the GSM interceptor will capture and record all incoming and outgoing traffic within the system's coverage zone, based on handsets IMEI. In Target mode the cell phone interception is based on IMSI and/or IMEI selection (only targets).
The interceptor supports subscriber (target) selection by the known IMSI and/or IMEI identifiers.
The "Target Correlation" function helps to identify the Target specific parameters from a list of all subscribers that were registered in the system. This function is intended to search for the target's IMEI identifier with the purpose of their subsequent use as selection parameters. This technique is based on comparing the lists of subscribers, registered in the internal (fake) network.
When equipped with the 3G add-on module, GSM interceptor is able to selectively downgrade 3G subscribers to 2G mode. This is achieved based on the subscriber's IMEI. Once in 2G mode, these downgraded subscribers are handled as any other GSM phone and can be intercepted, positioned etc.
This is the main threat to modern eavesdropping of a mobile phone (GSM) based conversation.

Über XCell Stealth Handys
For the security of your phone conversations, the XCell Stealth Phone allows you to achieve a high level of protection against the risks of interceptions, now more and more common when you use an unprotected mobile phone. Our phones are intended for protection of conversations against the control by the operator, and by any GSM interceptor. The phone will alert you if either an SMS / text message, outgoing or incoming call is made via such GSM interception technology. The XCell Stealth Phones guarantees that your calls and text messages are 100% confidential from any 3rd party interception or IMSI catchers. The phone will immediately alert you in real time of any attempt to intercept your communications. Handsets has been tested on such equipment as the Rohde & Schwarz type interceptors, Septier, Dominator, IBIS, GSS Pro-A, NeoSoft and few others. Our phones operates independantly of any server exchange data and instead uses a highly complex engine to ensure all incoming and outgoing calls are sweeped for a backdoor break in communication in real time.
XCell Stealth handsets are the perfect choice for politicians, lawyers, executives, police and government personnel, in fact anyone who recognises the need for complete secure communication.
The wiretaps can be based on the IMEI number or on the phone number. So in the case where the interception is performed starting from the knowledge of your IMEI number, change the SIM card there will be of no help, because it is the device itself to be intercepted.

The XCell Dynamic IMEI Phone is able to change IMEI code in different ways: systematically or manually, using simple procedures.
Changing the IMEI number manually, you can choose one to your liking. Alternatively, these identification numbers are generated automatically by the phone itself thanks to a sophisticated internal algorithm, and it is practically impossible that a number be repeated. In this way, the phone becomes in fact a new device every time, thus making its interception and localization impossible, and allowing you to speak freely without the risk of being heard or traced.
Unlike a cell phone that operates on the encrypted data item, codifying and making them unintelligible to any outside listener, the XCell Stealth Phone protects the call itself, making the phone untraceable, and impossible life for those who want to listen to it.
XCell Stealth Phone will alert you immediately, sending an alarm or a discrete vibration when someone tries to intercept you.
There are a variety of devices on the market today to encrypt your conversation. Though using of encryption to protect your privacy might be the prudent choice, the method has its own disadvantages:
A. You never know if encryption you use is indeed trustworthy and there is no reliable way to check it. Most of the encryption applications developers are not making public the source code. There can be (and most of the time there are) back doors used by law enforcement agencies.
Introducing a back door into a crypto system does not even require active cooperation of the manufacturer of the equipment. All it takes is one bribed programmer to compromise an entire product.
Some manufacturers of cryptographic equipment have a track record of hidden cooperation with intelligence agencies and interested private parties. Some of them are not even using publicly scrutinized and standardized crypto algorithms (like Diffie-Hellman, SHA256, AES and Twofish), but “proprietary” encryption methods that are not available for public evaluation. Several “proprietary” crypto-algorithms that were not subject to public review have been shown to be easily breakable in the past, like the COMP128 algorithm that is in use in many GSM networks for authentication, so the “proprietary crypto” approach has to be regarded as very risky.
B. Using of such devices might make you look suspicious and attract undesired attention to you.
C. If you are targeted by a intelligence agency, encrypting your mobile communications doesn't mean that you are 100% protected against eavesdropping. Think about that: will they drop you just because you are using encrypted communications? No, for sure.. Being a challange for them, will find another ways to get the info. Sure, for a short period of time your secrets will remain... secret. But any decent agency will find security breaches at any time, gathering info they need about you, by any means. Other exploitable intelligence sources are: human sources, disimulated bugs on your home, office and vehicle etc. Actually by encrypting your phone conversations, you are telling them that you have something important to hide and you are forcing agencies to use other ways to gather intelligence.
Better give them peace of mind by not using any encryption. Let them think that intercepting your calls by suppressing or breaking the A5/1 algorithm they can find out what they are looking for. Be smart and use on your advantage XCell Stealth phone: knowing if/when someone is tapping your voice calls and SMS, you can let them know what you want them to know. Smarter than encrypting your calls, on most cases.

D. An encrypted call is not so... encrypted, as you think. Even if you use a crypto phone, the GSM operator or the entity that operates a GSM interceptor can find out pretty much information such as:
- The phone number dialled by you or the phone number that is calling you. Hence, they can figure out the caller location and even his real identity. It is only a matter of time. They can (and they will do) tape his cell phone in order to find out who it is and what your relation with him is.
- The conversation length, time stamped.
- Your location at the moment of phone conversation.
- Your geographical location at every moment, by some simple and effective triangulation techniques.
Other crypto phone proven weaknesses:
- Some GSM interceptors can perform a DoS attack on your crypto phone, making that phone unavailable for use, for as long as they want. This occurs when crypto phone uses GPRS/data connection in order to transmit encrypted voice.
- Many modern GSM interceptors can downgrade your crypto phone connection from 3G to 2G, by simply jamming 3G uplink frequencies, which is a standard procedure. By doing that, many crypto phones that use data connections will fail and become useless.
- With carrier help, the phone IMEI can be blocked on the network.
- A GSM interceptor can perform a DoS attack on a BTS by continuously sending RACH bursts to all phones in the given area. This will affect all cell phones, including crypto phones from a certain area.
So, even if you use a crypto phone, there can be figured out the phone number and the person identity you are talking over the phone, your accurate locations, communication patterns etc. They will not know what you are talking about, but they will know when, for how long, where and who with. Sure, the voice call itself usually cannot be decrypted in a resonable period of time. But information above can be (and will be) used to find out in the end, your secrets.
That is why crypto phones can be used only for a short period of time as secure communication devices. In fact, being predictable is one of the worst choice on intelligence battlefield. And using a cryto phone means that you are more than predictable.
The only conclusion that you can make: instead of protecting your secretive communications in blind by using crypto phones, it is better to know when someone wants to find out your secrets and when they are trying to locate you. Then you can act advisedly, taking the right decisions and even influencing them by different deception techniques.
Do not assume that your secrets are hunted by various entities, all the time. This is not going to happen. Find out exactly when you are a target and for how long.
A5/0, A5/1, A5/2, A5/3
The GSM ciphering algorithm is called A5. There are four variants of A5 in GSM, only first three of which are widely deployed:
A5/0: no ciphering at all
A5/1: strong(er) ciphering, intended for use in North America and Europe
A5/2: weak ciphering, intended for use in other parts of the world, but now deprecated by the GSMA
A5/3: even stronger ciphering with open design
A5/1
Is a stream cipher used to provide over-the-air communication privacy in the GSM cellular telephone standard. It was initially kept secret, but became public knowledge through leaks and reverse engineering. A number of serious weaknesses in the cipher have been identified. A5/1 is used in Europe and the United States.
A5/2
Is a stream cipher used to provide voice privacy in the GSM cellular telephone protocol. A5/2 was a deliberate weakening of the algorithm for certain export regions. The cipher is based around a combination of four linear feedback shift registers with irregular clocking and a non-linear combiner.
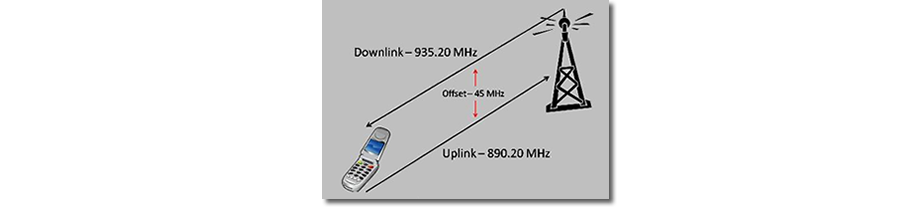
ARFCN
In GSM cellular networks, an absolute radio-frequency channel number (ARFCN) is a code that specifies a pair of physical radio carriers used for transmission and reception in a land mobile radio system, one for the uplink signal and one for the downlink signal. This network parameter is used to force the cell phones to send registration requests to a false BTS (IMEI/IMSI catcher).
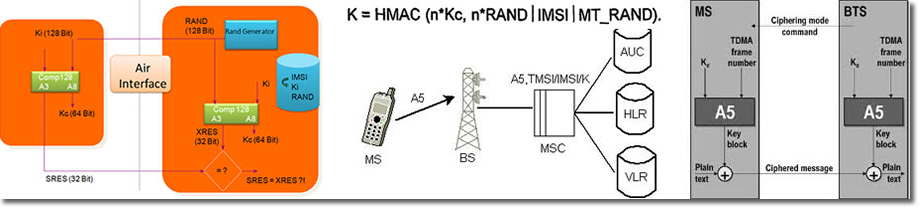
Authentication Key (Ki)
The authentication key or Ki is a 128 bit key used in the authentication and cipher key generation process. In a nutshell, the key is used to authenticate the SIM on the GSM network. Each SIM contains this key which is assigned to it by the operator during the personalization process. The SIM card is specially designed so the Ki can't be compromised using a smart-card interface.
Ciphering Key (Kc)
The SIM contains the ciphering key generating algorithm (A8) which is used to produce the 64-bit ciphering key (Kc). The ciphering key is computed by applying the same random number (RAND) used in the authentication process to the ciphering key generating algorithm (A8) with the individual subscriber authentication key (Ki). The ciphering key (Kc) is used to encrypt and decrypt the data between the MS and BS. However, a passive GSM interceptor can extract and calculate remotely the Ciphering Key and using it for deciphering in real time.
BCCH
A broadcast control channel (BCCH) is a point to multipoint, unidirectional (downlink) channel used in the Um interface of the GSM cellular standard. The BCCH carries a repeating pattern of system information messages that describe the identity, configuration and available features of the base transceiver station (BTS).
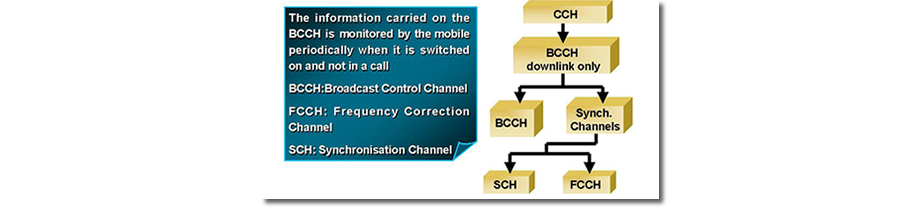
BCCH manipulation
A special technique. GSM interceptors (IMEI/IMSI catchers) uses BCCH manipulation to give a "virtual power" effect of up to several hundred watts. By doing that, a GSM interceptor will trick the handsets, which will always choose the "BTS" with the strongest signal. As well, by changing Cell ID (all other network parameters remains the same - MCC, MNC, LAC) and ARFCN, the interceptor is forcing the cell phones within the area to send registration requests, collecting this way phones identifiers: IMSI, IMEI, classmark, etc.
BTS
The base transceiver station contains the equipment for transmitting and receiving radio signals (transceivers), antennas, and equipment for encrypting and decrypting communications with the base station controller (BSC).

Carrier
A company that provides GSM telecommunications services.
Cell
In personal communications systems (cellular mobile phone systems) a cell is the geographic area served by a single base station. Cells are arranged so that base-station frequencies can be reused between cells. The area surrounding a cell site. The area in which calls are handled by a particular cell site.
Cell ID
A GSM Cell ID (CID) is a generally unique number used to identify each Base transceiver station (BTS) or sector of a BTS within a Location area code (LAC) if not within a GSM network. In some cases the last digit of CID represents cells' Sector ID. This network parameter is used in so called BCCH manipulation by GSM interceptors. By changing Cell ID (all other network parameters remains the same - MCC, MNC, LAC) and ARFCN, the system is forcing the cell phones within the area to send registration requests, collecting this way phones identifiers: IMSI, IMEI, classmark, etc.
Cell Site
The transmission and reception equipment, including the base station antenna, that connects a cellular phone to the network.
Channel Coding
Channel coding is the technique of protecting message signals from signal impairments by adding redundancy to the message signal.
Fade
A fade is a slow change in signal strength.
GSM 1800
The GSM 1800 band provides for a GSM uplink in the range 1710-1785 MHz, a a GSM downlink in the range 1805-1880 MHz.
GSM 1900
The GSM 1800 band provides for a GSM uplink in the range 1850-1910 MHz, a a GSM downlink in the range 1930-1990 MHz.
GSM 900
The GSM 900 band provides for a GSM uplink in the range 890-915 MHz, a a GSM downlink in the range 935-960 MHz.
GSM Air Interface
The GSM air interface operates in the UHF frequency band.
GSM Architecture
A GSM network consists of the mobile station, the base station system, the switching system, and the operation and support system.
GSM Base Station System (BSS) The GSM base station system (BSS) provides the interface between the GSM mobile phone and other parts of the GSM network.
GSM Channels
GSM provides two types of channel: traffic channels and signalling channels
GSM Handover
Handover refers to the process by which a GSM mobile phone's affiliation is transferred from one base station to another.
GSM Interceptor
See IMEI/IMSI catcher.
GSM Security
GSM provides a number of security services, including authentication, key generation, encryption and limited privacy.
IMEI
The International Mobile Station Equipment Identity or IMEI is a number, usually unique, to identify 3GPP (i.e., GSM, UMTS and LTE) and iDEN mobile phones, as well as some satellite phones. The IMEI number is used by a GSM network to identify valid devices and is only used for identifying the device and has no permanent or semi-permanent relation to the subscriber. It is also used by IMEI/IMSI catchers / GSM interceptors in order to identify your phone and performing call interception.
IMSI
The International Mobile Subscriber Identity is a unique identification associated with all cellular networks. It is stored as a 64 bit field and is sent by the phone to the network. It is also used for acquiring other details of the mobile in the home location register (HLR) or as locally copied in the visitor location register. To prevent eavesdroppers identifying and tracking the subscriber on the radio interface, the IMSI is sent as rarely as possible and a randomly generated TMSI is sent instead.
IMSI catcher
Is essentially a false mobile tower acting between the target mobile phone(s) and the service providers real towers. As such it is considered a Man In the Middle (MITM) attack. It is used as an eavesdropping device used for interception and tracking of cellular phones and usually is undetectable for the users of mobile phones. Such a virtual base transceiver station (VBTS) is a device for identifying the International Mobile Subscriber Identity (IMSI) of a nearby GSM mobile phone and intercepting its calls.
The IMSI catcher masquerades as a base station and logs the IMSI numbers of all the mobile stations in the area, as they attempt to attach to the IMSI-catcher. It allows forcing the mobile phone connected to it to use no call encryption (i.e., it is forced into A5/0 mode), making the call data easy to intercept and convert to audio.

LAC
Location Area Code, unique number broadcast by a "base transceiver station" in GSM. A "location area" is a set of base stations that are grouped together to optimise signalling. Typically, tens or even hundreds of base stations share a single Base Station Controller (BSC) in GSM, or a Radio Network Controller (RNC) in UMTS, the intelligence behind the base stations. The BSC handles allocation of radio channels, receives measurements from the mobile phones, controls handovers from base station to base station.
MCC
Mobile country code, used in wireless telephone network station addressing.
MNC
A mobile network code (MNC) is used in combination with a mobile country code (MCC) (also known as a "MCC / MNC tuple") to uniquely identify a mobile phone operator/carrier using the GSM/LTE, CDMA, iDEN, TETRA and UMTS public land mobile networks and some satellite mobile networks.
MSISDN
Is a number uniquely identifying a subscription in a GSM or a UMTS mobile network. Simply put, it is the telephone number to the SIM card in a mobile/cellular phone. This abbreviation has several interpretations, the most common one being "Mobile Subscriber Integrated Services Digital Network-Number". See also Silent Call.
SIM Card
Smart card that gives GSM phones their user identity. SIM cards make it easy for phones to be rented or borrowed.
Silent Call
In terms of GSM interception, a silent call is a call originated from the GSM interceptor to a specific IMEI/IMSI, in order to make correlations between IMEI/IMSI and MSISDN (Mobile Subscriber Integrated Services Digital Network-Number, which is actually the telephone number to the SIM card in a mobile/cellular phone). By using the silent call, an GSM interceptor can find out a certain phone number alocated to a specific IMEI/IMSI. Silent calls are a result of process known as pinging. This is very similar to an Internet Protocol (IP) ping. A silent call cannot be detected by a phone user. Not to be confused with Spy Call, which mean listen to phone surroundings.

Silent SMS
Many foreign police and intelligence services use clandestine "Silent" SMS to locate suspects or missing persons. This method involves sending an SMS text message to the mobile phone of a suspect, an SMS that goes unnoticed and sends back a signal to the sender of the message.
Also known as Flash-SMS, the Silent SMS uses an invisible return signal, or "ping". Developers from the Silent Services company, who created some of the first software for sending this type of SMS, explain: "The Silent SMS allows the user to send a message to another mobile without the knowledge of the recipient mobile's owner. The message is rejected by the recipient mobile, and leaves no trace. In return, the sender gets a message from a mobile operator confirming that the Silent SMS has been received."
Silent SMS were originally intended to allow operators to ascertain whether a mobile phone is switched on and to "test" the network, without alerting the users. But now, intelligence services and police have found some other uses for the system. Neil Croft, a graduate of the Department of Computer Science at the University of Pretoria in South Africa, explains: "Sending a Silent SMS is like sending a normal SMS, except that the mobile does not see the message it has received. The SMS's information is modified, within the data coding scheme, so that the user who receives the message doesn't notice anything. A Silent SMS can help police to detect a mobile without the person concerned being aware of the request."
Technical bit: in order to tamper with the SMS's information and make it silent, the security services go through a network for sending and receiving SMS known as an SMS gateway, such as the Jataayu SMS gateway. This allows them to interconnect the processing and GSM systems. This method of mass sending appears to be widely used by these security services. In November 2011, Anna Conrad of the Die Linke (The Left) party in Germany, posed a written question to her local state assembly concerning the use of Silent SMS by the German police. Her local assembly responded: in 2010, her state conducted 778 investigations and sent 256,000 Silent SMS.
Mathias Monroy, a journalist with Heise Online, argues this surveillance technology is flourishing largely as a result of a legal vacuum: "This is very problematic for privacy, because legally it is unclear whether or not a Silent SMS counts as a communication (…) The state found that it was not one, since there is no content. This is useful, because if it is not a communication, it does not fall under the framework of the inviolability of telecommunications described in Article 10 of the German Constitution."
On December 6, the German Interior Minister Hans-Peter Friedrich announced that German police and intelligence had been sending an average of 440,000 Silent SMS a year since they began using the system. After each SMS was sent, investigators went to the four German mobile operators – Vodafone, E-Plus, O2 and T-Mobile – in order to access the recipient's information. To aggregate this raw data provided by operators, the police use Koyote and rsCase, software supplied by Rola Security Solutions, a company that develops "software solutions for the police".
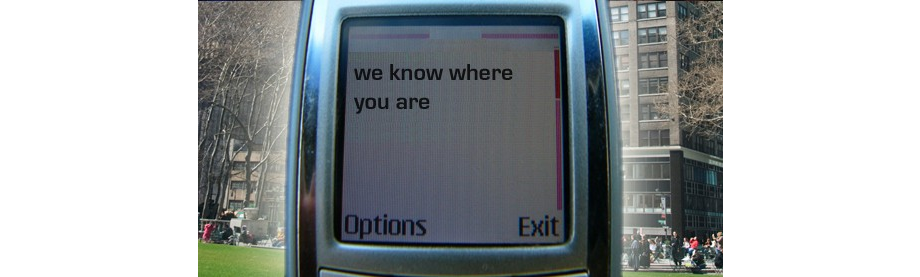
Silent SMS allow the user to precisely locate a mobile phone by using the GSM network, as Karsten Nohl explains: "We can locate a user by identifying the three antennas closest to his mobile, then triangulating the distance according to the speed it takes for a signal to make a return trip. A mobile phone updates its presence on the network regularly, but when the person moves, the information is not updated immediately. By sending a Silent SMS, the location of the mobile is instantly updated. This is very useful because it allows you to locate someone at a given time, depending on the airwaves."
This technique is much more effective than a simple cellular location (Cell ID), as François-Bernard Huyghe, a researcher at IRIS, sets out: "This is the only instantaneous and practical method to track a mobile constantly when it's not in use. We're talking then about geopositioning rather than geolocation. After that, either the police track the information via the operators, or private companies process the data and, for example, refer the investigator to a map where the movements of the monitored phone appear in real time."
The benefits of Silent SMS don't stop there: by sending a large number of these SMS, security services can also disrupt the mobile or remotely reactivate its signal and wear out the battery. A spokesman for the German Interior Ministry tells OWNI: "German police and intelligence services use Silent SMS to reactivate inactive mobile phones and refine the geolocation of a suspect, for example when they move during an interview. The Silent SMS is a valuable investigative tool, which is used only as part of a telecommunications surveillance operation sanctioned by a judge, in a specific case, without violating the fundamental right to protection of privacy."
In France, police and intelligence services work with Deveryware, a "geolocation operator". Deveryware also market a "geolocation employee punchcard", the Geohub, to businesses. Deveryware combine cellular localization, GPS, and other "real-time location" techniques. Questioned by OWNI whether Silent SMS were one of these techniques, the company's response was evasive: "Regretfully we are unable to provide an answer, given the confidentiality imposed on us by legal requisitions." Deveryware's applications enable investigators to map and compile a history of a suspect's movements. Laurent Ysern, head of investigations for SGP Police, states: "All investigative services have access to the Deveryware platform. With this system, one can follow a person without having to be behind them. There's no need for shadowing, so less staff and equipment needs to be mobilized."
While in Germany the Ministry of the Interior responded within 48 hours, the French government remains strangely silent. There has been one single response, from the Press Department of the National Police: "Unfortunately, no one at the PJ (Police Judiciare) or the public safety office is willing to comment on the subject, these are investigative techniques …"
Silence too from the French telecoms operators SFR and Bouygues Telecom. Sebastien Crozier, a union delegate at France Telecom-Orange, says: "Operators always collaborate with the police, it's a public service obligation: they act in accordance with judicial requests…There is no definitive method, sending SMS is one of the methods used to geolocate a user. We mainly use this technique to "reactivate" the phone."
By 2013, the use of these surveillance methods is expected to reach an industrial scale. The Department of Justice will set up, with the help of the arms company Thales, a new national platform of judicial interception (PNIJ), which is expected to centralize all legal interception, i.e, phone-tapping, but also summons such as requests for cell location. Sebastien Crozier remarks: "This interface between police officers and operators will streamline court costs and reduce processing costs by half, because until now summons have been handled station by station…There will be more applications, but it will be less expensive for operators like the police." source
When using XCell Stealth phones you can block silent SMS simply by deleting SMS center number, stored on phone memory. Go to Menu > Messages > Settings > Text messages > Sending options > Service center > delete the service center number > press Save > Exit.
Please note that by deleting that phone number, you will not be able to send any SMS.
If you want to know if someone is trying to locate you by sending silent SMS, activate UnPing feature and then go to main
menu > my files > other files > log.txt. All data is date/time/detail stamped. There you can find if someone is trying to locate your phone, when was doing that (time, date) and how many times was trying to locate you.
A Spy Call is a call made from a GSM interceptor to a mobile phone, in order to listen to phone surroundings. This call cannot be detected by the phone user.

TMSI
The Temporary Mobile Subscriber Identity (TMSI) is the identity that is most commonly sent between the mobile and the network. TMSI is randomly assigned by the VLR to every mobile in the area, the moment it is switched on. The number is local to a location area, and so it has to be updated each time the mobile moves to a new geographical area.
The network can also change the TMSI of the mobile at any time. And it normally does so, in order to avoid the subscriber from being identified, and tracked by eavesdroppers on the radio interface. This makes it difficult to trace which mobile is which, except briefly, when the mobile is just switched on, or when the data in the mobile becomes invalid for one reason or another. At that point, the global "international mobile subscriber identity" (IMSI) must be sent to the network. The IMSI is sent as rarely as possible, to avoid it being identified and tracked.
How does the pinpointing of mobile users work, and just how accurate is it?
There are two methods for pinpointing the location of cell phone users. Cell phones equipped with Global Positioning System (GPS) capability, use signals from satellites to pinpoint location very accurately. The second, and less-accurate method is often called “Cell Tower Triangulation”, referring to how the cell towers which receive a phone’s signal may be used to calculate its geophysical location.
According to some industry research estimates, only about 11% of phones manufactured this year will have the GPS capability, so the remaining 89% of phones without GPS would have to depend upon “Cell Tower Triangulation” in order to disclose geolocation data for applications.
Just what is Cell Tower Triangulation?
In a best-case-scenario, a cell phone's signal may be picked up by three or more cell towers, enabling the "triangulation" to work. From a geometric/mathematical standpoint, if you have the distance to an item from each of three distinct points, you can compute the approximate location of that item in relation to the three reference points. This geometric calculation applies in the case of cell phones, since we know the locations of the cell towers which receive the phone's signal, and we can estimate the distance of the phone from each of those antennae towers, based upon the lag time between when the tower sends a ping to the phone and receives the answering ping back.
In many cases, there may actually be more than three cell towers receiving a phone’s signal, allowing for even greater degrees of accuracy (although the term “triangulation” isn’t really correct if you’re using more than three reference points). In densely developed, urban areas, the accuracy of cell phone pinpointing is considered to be very high because there are typically more cell towers with their signal coverage areas overlapping. In cases where a cell user is inside large structures or underground, cell tower triangulation may be the only location pinpointing method since GPS signal may not be available.
For many cell tower networks, the pinpointing accuracy may be even greater, since directional antennae may be used on the tower, and thus the direction of the cell phone’s signal might be identifiable. With the signal direction plus the distance of the phone from the cell tower, accuracy might be pretty good, even with only two towers.
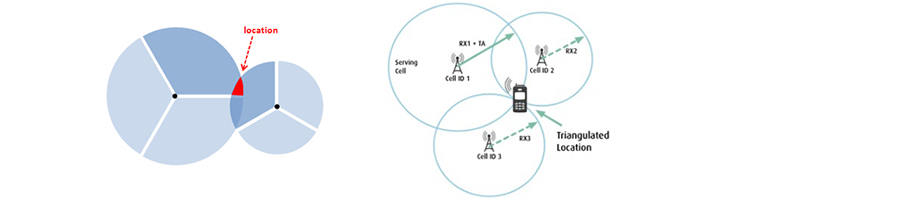
However, there are many places where there are fewer cell towers available, such as in the fringes of the cities and out in the country. If you have fewer than three cell towers available, pinpointing a mobile device can become a lot less precise. In cities where there are a lot more vertical structures which can be barriers to cell phone broadcasting and receiving, there have to be many more cell towers distributed in order to have good service. In the countryside, there are relatively fewer cell towers and a phone's signal may be picked up only by a single one at much greater distance.
Those areas where a phone is only getting picked up by a single tower, and if it's equipped with only omnidirectional antennae, the accuracy becomes even less. In rural areas, coverage of the cell tower can vary from about a quarter of a mile to several miles, depending upon how many obstacles could be blocking the tower's signal.
How extensive is government monitoring?
No civilian is authorised to know. Some governments in the EU, such as the UK government, have laws and practices that allow the government to collect and use intelligence in legal cases without disclosing their sources or methods. Chapter 8 of the Crown Prosecution Service’s Disclosure Manual includes: “the ability of the law enforcement agencies to fight crime by the use of covert human intelligence sources, undercover operations, covert surveillance, etc” and “the protection of secret methods of detecting and fighting crime”.
According estimates made by whistleblower William Binney, a former director of the US NSA’s World Geopolitical and Military Analysis Reporting Group), the US NSA alone has assembled 20 trillion “transactions” − phone calls, emails and other forms of data − just from Americans (April, 2012). Government agencies are not the only organisations interested in the personal data stored on, or transmitted through, your mobile phone. Self-styled cyber criminals are now jumping on the bandwagon to reap benefits previously enjoyed only by government and intelligence agencies.
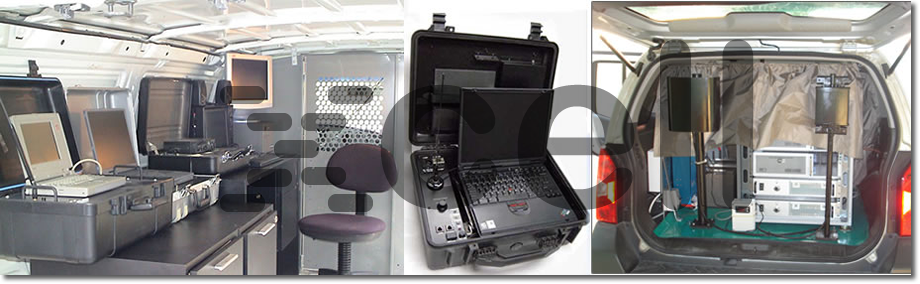
Target phone location performed by GSM interceptor with target location capabilities.
The method of operation is based on two vehicles. First vehicle with the interception system that forces the target phone to send continues signal transmission. The second vehicle is deployed with the interceptor and location components. The direction to target is displayed as a compass pointer and the relative signal strength is shown as a bar graph and numerically. The audio tone increases in frequency as interceptor gets closer to the target giving a clear warning of a close encounter.
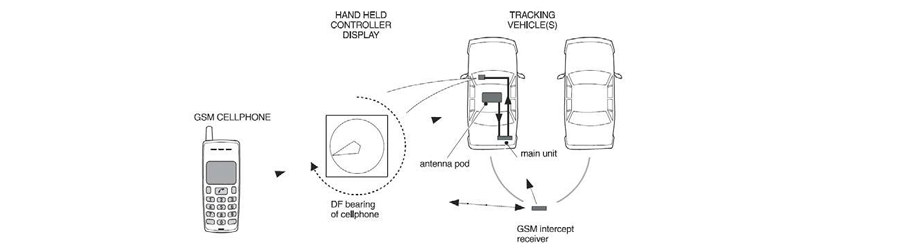
Xcell Dynamic IMEI phones will detect in real time this continuos signal transmission, as an abnormal number of GSM network re-registration requests. When a ping is detected coming from the network or from a GSM interceptor like above, then the user will be alerted.
DISCLAIMER:
The company is not responsible for the IMEI change. The phone comes with original IMEI and any changes are under the direct control of the customer. Actually the original IMEI is never changed, but only the one provided for the mobile network or GSM interceptor, which is a random virtual IMEI. In addition, the device is made available only for alerting in case of interceptions by third parties. The company is exempted from liability for any misuse.



